What Is Attribute-Based Access Control (ABAC)?
- Share:




2938 Members
When building an application, there is one crucial thing we have to make sure of: The right people have the right access to the right assets. This is what authorization is all about.
While Role Based Access Control (RBAC) determines access based on predefined roles (Like Admin, Editor, and Viewer, for example), Attribute Based Access Control (ABAC) deals with, you guessed it - attributes.
The use of ABAC aligns with the growing complexity and diversity of modern applications, where conventional access control methods fail to address intricate, ever-changing security requirements.
In this blog, we'll see how ABAC can help you tackle these challenges by enabling highly fine-grained authorization policies.
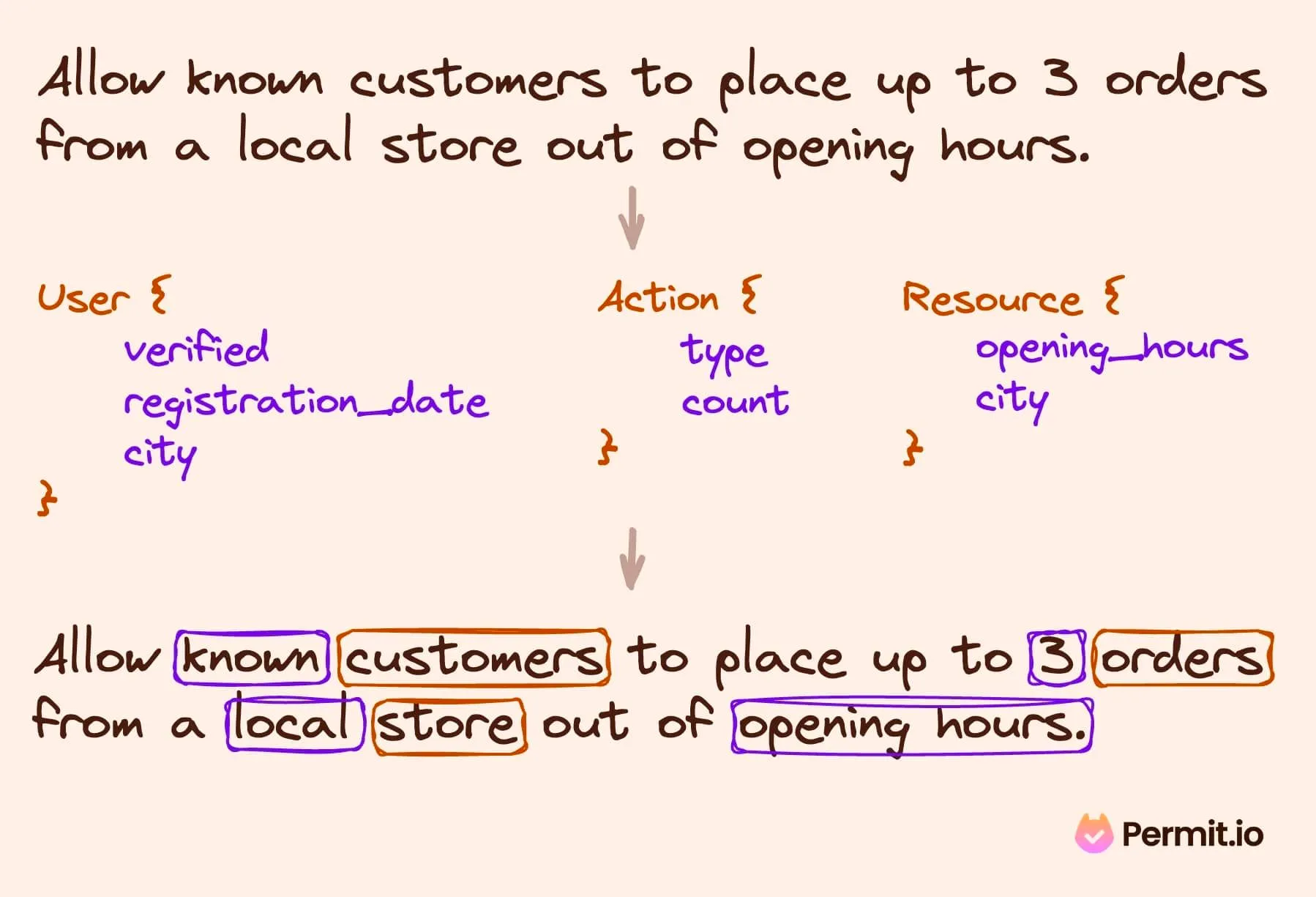
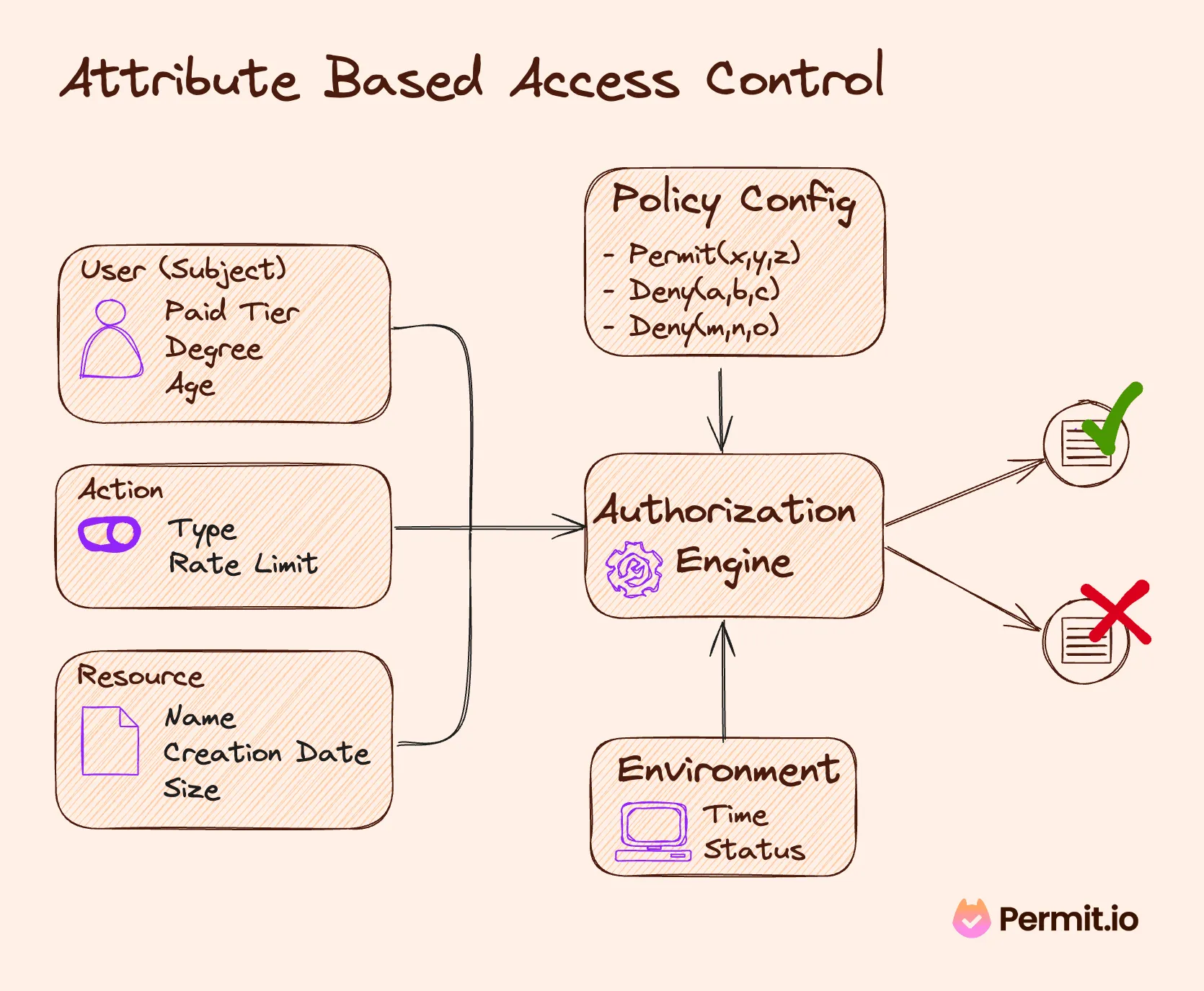
Attribute Based Access Control determines access based on conditions applied to attributes (or characteristics) rather than roles, allowing the definition of fine-grained complex access-control rules.
ABAC adapts to complex, distributed environments, making it ideal for applications requiring high customization and contextual sensitivity in access decisions. It thrives in scenarios where user roles are insufficient to capture the full spectrum of access needs. Let’s look at an example -
An ABAC policy is crafted using a combination of subject, resource, action, and attributes. By considering these four elements, an ABAC policy can reach the Boolean decision of access granted/denied.
There are four types of attributes that the ABAC model utilizes to craft access policies. An ABAC policy can use one or all of them together, depending on the context and the policy requirements:
The ABAC framework integrates these components to create a rich, multi-dimensional approach to access control, enabling precise and adaptable policies for varying scenarios.
ABAC offers several compelling advantages:
Each of these benefits illustrates how ABAC's nuanced approach to access control can be practically applied across various sectors, showcasing its versatility and effectiveness in addressing complex security challenges.
Adopting ABAC offers many benefits, but it's essential to be aware of its challenges:
Effectively addressing these challenges is crucial for organizations to harness the full potential of ABAC, ensuring an efficient, flexible access control system.
ABAC's approach to access control is distinct from other models like RBAC (Role-Based Access Control), ReBAC (Relationship-Based Access Control), and PBAC (Policy-Based Access Control).
RBAC (Role-Based Access Control) focuses on predefined roles with set privileges, while ABAC introduces a multi-attribute framework for more dynamic decision-making. For instance, in RBAC, a 'manager' role may have broad access within a department. Still, ABAC can refine this by considering additional attributes like project assignment or location, offering more tailored access.
ReBAC (Relationship-Based Access Control) adds another dimension to access control by considering relationships between entities. For example, in a social networking platform, access control might depend on the nature of the user relationships (like friends or followers). While versatile in evaluating multiple attributes, ABAC doesn't inherently account for these relational dynamics.
ABAC is often seen as a specialized form of [**PBAC (Policy-Based Access Control)**](https://www.permit.io/blog/what-is-rbac#:~:text=Policy-Based Access Control (PBAC) "https://www.permit.io/blog/what-is-rbac#:~:text=Policy-Based Access Control (PBAC)"), focusing on leveraging a wide range of attributes for access decisions. PBAC encompasses broader policy-based controls, but ABAC differentiates itself with its fine-grained, attribute-centric approach.
Each model has its strengths, and the choice depends on your application's specific requirements and the organizational context.
package abac
# User attributes
user_attributes := {
"User1": {"location": "EU", "title": "employee"},
"User2": {"location": "US", "title": "employee"},
"User3": {"location": "EU", "title": "manager"}
}
# Document attributes
document_attributes := {
"Doc1": {"classification": "GDPR Protected"},
"Doc2": {"classification": "Non-sensitive"}
}
# Default deny
default allow = false
# EU employees can perform any action on GDPR Protected Document
allow {
# Lookup the user's attributes
user := user_attributes[input.user]
# Check that the user is an employee
user.title == "employee"
# Check that the employee is based in the EU
user.location == "EU"
# Check that the document is GDPR Protected
document_attributes[input.document].classification == "GDPR Protected"
}
# Allow any employee to access non-GDPR-protected documents
allow {
# Lookup the user's attributes
user := user_attributes[input.user]
# Check that the user is an employee
user.title == "employee"
# Lookup the document's attributes
document := document_attributes[input.document]
# Check that the document is not GDPR Protected
document.classification = "Non-sensitive"
}
An example of OPA’s Rego code declares ABAC as Policy
Choosing the appropriate access control model depends on various factors, such as the organization's size, complexity, and the specific nature of the access requirements. RBAC might suffice for a small business with well-defined roles and limited scope. However, in a large, dynamic enterprise with diverse and evolving access needs, the flexibility and granularity of ABAC could be more beneficial.
Organizations often start by implementing their own RBAC and then gradually evolve it into ABAC as additional attributes are required. When dynamic data points such as time, location, billing status, and current behavior come into effect - ABAC is unavoidable.
At the end of the day, authorization models are more thinking tools than concrete guidelines, and most applications end up mixing between them (especially as time passes and the applications evolve). The most important thing is how you design them so that they're flexible, scalable, and continue to evolve along with your application's needs.
By implementing and managing your RBAC, ABAC, or ReBAC policies using an authorization service that allows for flexible transition between authorization models and provides a simple API and no-code UI that makes permission management accessible to all stakeholders.
Permit provides developers with a permission management solution that allows for smooth transitioning between RBAC, ABAC, or ReBAC without any changes to your application code and the ability to create and manage policies using an accessible no-code UI.
Permit’s UI allows us to define our required roles, attributes, and role derivation logic. It generates code for us and pushes any updates or changes to our application in real time. Implementing authorization with Permit ensures everyone is included in the permission management process, preventing developers from becoming bottlenecks.
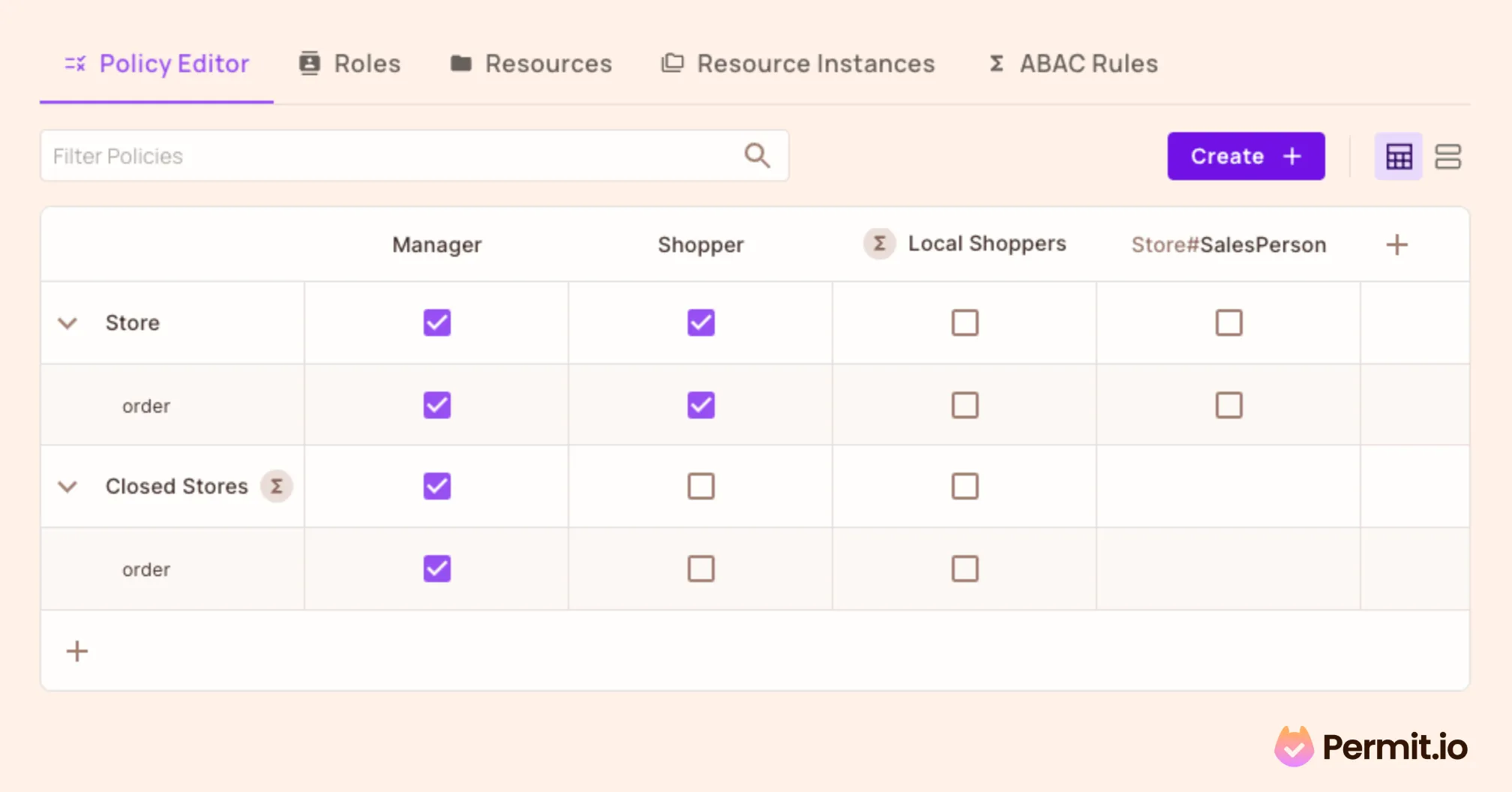
An example of Permit.io's hybrid policy editor combines RBAC, ABAC, and ReBAC in one interface.
ABAC is crucial to access control, offering unparalleled flexibility and precision. Its adoption is especially beneficial for developers navigating the complexities of modern applications seeking robust, adaptable, and efficient access control.
Want to learn more about Authorization? Join our Slack community, where thousands of devs are discussing, building, and implementing access control for their applications.
More ABAC-Related Resources are available here:

Full-Stack Software Technical Leader | Security, JavaScript, DevRel, OPA | Writer and Public Speaker